I would like to talk about what two-factor authentication (2FA) is and why you should use it. If you want to keep your online accounts secure (Banks, emails, cloud services, games, etc), I recommend you keep reading.
2FA is an additional layer of security for the account, beyond simply a username and password. A second credential, in addition to the password, is required to gain access to the account. Each time an account is logged in with a password, and the app sends a code to the phone to confirm the identity of the person logging in, 2FA has been used.
Even if a person knows your credentials (username and password), if they do not have the code or token generated by 2FA, they will not be able to access your account. That is why it is so important.
Who release the first two-factor authentication (2FA)?
The concept of two-factor authentication (2FA) has been around for several decades, but it was not widely used until recently. The first two-factor hardware-based authentication system was developed in the 1980s by a company called RSA Security, which created a hardware token that generated a one-time password (OTP) for each login attempt.

RSA SecurID, the first two-factor hardware-based authentication system.
This hardware token was widely adopted by banks, governments, and other organizations that required a higher level of security for their users. Over time, 2FA has evolved and now includes various methods such as software tokens, text message-based authentication, biometrics, and others.
Overall, while 2FA tokens provide an additional layer of security, they are not foolproof and can be vulnerable to attacks if not managed and implemented properly. It is important to keep in mind that 2FA should be used in combination with other security measures, such as strong passwords, secure communication channels, and regular software updates.
How does two-factor Authentication (2FA) work?
In order not to make it too complicated to understand, we will use this small diagram that everyone can understand.
- Login: The user introduces their username/password and logs in correctly.
- Authentication: The system triggers the two-step authentication process and prompts the user to enter the token that you will receive by SMS, phone call, app or with a FIDO key.
- Access: The token is correct, and you log in to your user account.
The security lies in the fact that even if an attacker obtains your username/password, without the token they will not be able to access your account.
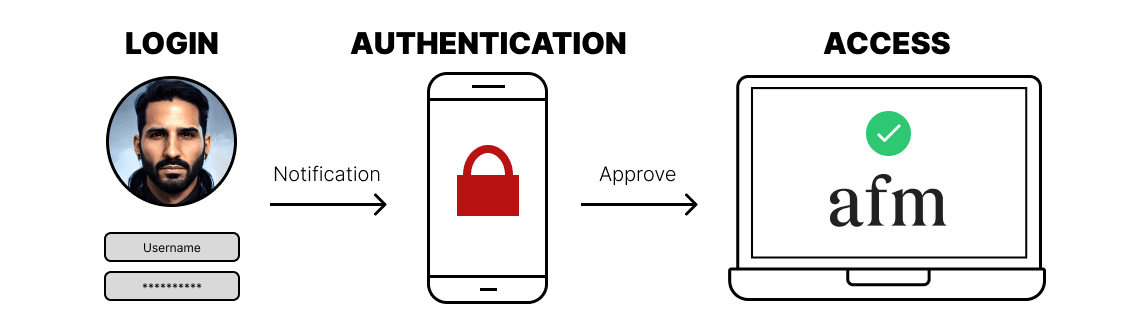
Simple 2FA Flowchart
How many two-factor authentication (2FA) methods are currently available?
- SMS: you receive a unique code to your phone number via SMS.
- Phone call: you receive a unique code to your phone number via a phone call.
- App/Application: the code is obtained from an application on your mobile phone. The application generates unique codes that change every 30 or 60 seconds (depending on the platform).
- Mobile notification: a notification that may appear on your phone or in an application asking you whether you authorize access to your account.
- FIDO2 key: enables strong multi-factor authentication without a password. The procedure is based on the principles of asymmetric encryption.
- Recovery codes: this is an emergency code that can be used in case any of the above options do not work properly. Whether you lose your line or network, delete the app, or lose access to your phone.
- Biometric factors: Access by fingerprint, facial or voice recognition.
Don’t forget that it is also essential to use a strong password and not repeat it on multiple accounts, don’t install software of questionable origin and don’t log into your important accounts (banking, email, games or whatever) from someone else’s device. You never know what kind of virus, malware or spyware may be installed on a computer you have never used before.
Some of the best 2FA methods are:
Authy (The best)
Authy from Twilio is free and supports multiple devices. By transmitting a one-time password (OTP) to your desktop or mobile device and syncing it directly with the website or service to grant you access, Authy improves your online security.

💡 Authy is more sophisticated than Google Authenticator since it includes extra features like cloud backup, multiple device synchronization, secure file storage, and the ability to limit access to the app with a fingerprint, ensuring that we are the ones using it. Strongly suggested.
YubiKey (FIDO2 Key)
The YubiKey, manufactured by Yubico, is a hardware authentication tool that supports one-time passwords (OTP), public-key cryptography, authentication, the Universal 2nd Factor (U2F), and FIDO2 protocols to secure access to computers, networks, and online services.

💡 Most services allow you to simultaneously set up 2FA protection via an app or a key, such as YubiKey. If for some reason you don’t have your phone available, you can use the YubiKey key as an alternative validation method to access your account.
Microsoft Authenticator
Microsoft Authenticator is a software that uses two-step verification to improve account security and give a safe way to sign in. It is compatible with services like as Outlook, Microsoft 365, Azure, GitHub, and others. It provides one-touch sign-in, simple device management, and enhanced security features.

💡 It also provides additional protection by allowing us to customize the fingerprint or face to access the program, offering an additional degree of security to the application’s use.
Google Authenticator
Google Authenticator is application that adds an extra layer of protection to internet accounts. It produces one-time passwords (OTPs), which, combined with your login and password, are required to access the account. It protects your accounts by preventing unauthorized access.

💡 One of the most well-known, but if you lose your phone and don’t have the security keys to restore a backup, you’ll have to go through the time-consuming process of resetting 2FA on all accounts where it was enabled.
FreeOTP (Open Source)
FreeOTP is a two-factor authentication tool for systems that use one-time password protocols, including Android and iOS compatibility. Tokens may be readily added by scanning a QR code or inputting the token setup manually. FreeOTP uses open standards. This implies that there is no need for a proprietary server-side component; instead, utilize any server-side component that implements these standards.

💡 If you don’t like proprietary software, the best open source alternative at the moment is FreeOTP.
GNOME Authenticator (Linux)
Gnome Authenticator is a 2-factor authentication code generator for Linux desktops such as Ubuntu. It can produce two-factor authentication tokens for over 500 well-known providers, including GitHub, GitLab, Twitter, Facebook, Google, Dropbox, and Twitch.



